ELI5: SAML

What is SAML?
Security Assertion Markup Language (SAML), pronounced like sam-mull, is an authentication feature that grants users access to different company web applications using their employee login credentials. It’s a version of single sign on (SSO), where a user can log into one account in order to access another service automatically. A familiar form of SSO is social login, where users verify their identity via their social network, like Google or Facebook. Similarly with SAML, also called ‘Enterprise SSO’, users sign in once via their workplace identity provider (IdP) and are then able to access any website their business has specifically integrated with.
The two main entities in SAML are:
- The service provider (SP) is the entity or website providing the service or application, such as Salesforce, Jira, and Zendesk.
- The identity provider (IdP) is used by companies to manage their employees, similar to a directory. Okta, Azure AD, JumpCloud, Rippling, and Google are well-known IdPs.
Now what does this look like in real life? Let’s say Jake just started his new job at WonderWorld Inc. He’s given a work email, jake@wonderworld.com, and signs into his company’s Google account. Next, he clicks to open JIRA and is immediately in his team’s JIRA dashboard. Then he clicks on the Salesforce icon and, again, is on his team’s Salesforce dashboard. All without needing to enter his credentials again. How does this work? WonderWorld set up SAML connections with both JIRA, Salesforce, giving all their employees access.

Does Your Business Need SAML?
Now that we see how SAML is used in the real world, we need to determine if it’s necessary for your business. To do so, let’s go over SAML’s main benefits for each different ‘players’: the employee, the employee’s company (via an IdP), and the service provider.
Employee:
- Employees’ main benefits are an improved user experience. While logging into a website is usually a quick task, there are potential challenges, such as forgetting your password. By requiring employees to login just once via their IdP, SAML eliminates any room for error in subsequent logins. This guarantees that the employee has frictionless and instantaneous login experiences throughout their day.
Employee’s Company:
- Companies choose to use SAML because it significantly improves their security in a number of ways. First, it helps them automate their employee onboarding and off-boarding processes. For large companies that use multiple apps, it’s a security risk to manually grant and revoke privileges whenever someone joins or leaves. Most concerning, there’s a high probability someone will forget to remove an ex-employee from an app, thus allowing them to continue to access private information. Instead with SAML, the company can streamline employee management tasks via one source-of-truth platform, their IdP, reducing the risk of human error.
- Another security benefit of SAML is by coupling the IdP’s access with the SPs’ access, the company eliminates the need for each employee to have a different password for every SP. Because most people use weak, simple passwords and repeat them across multiple sites, without SAML, the company is more vulnerable to breaches and hacks. With SAML, employees only have to remember one, preferably strong login to access all their applications.
Service Provider:
- Given the employee and company benefits listed above, the vast majority of large enterprise companies rely on SAML—and thus require any new product they purchase to be SAML based. Simply put, if you’re a B2B businesses looking for enterprise-level customers, you’re going to need SAML to be market ready. Even if your app is the best available, many enterprises will simply not work or even continue discussions with a company that doesn’t support SAML.

As a Service Provider: Build or Buy?
Now that we know how important SAML is, the next question is if you’re a service provider, should you build or buy? It depends on your authentication experience and how you want to prioritize your resources. SAML is notoriously complicated and even with prior auth experience, will take a significant amount of time to set up as each IdP has its own unique configuration. In our biased opinion, building SAML yourself is likely more work than you want to take on, especially if you’re a startup. It’s probably more important for your developers to focus on building your MVP or client-requested features instead of spending weeks or months on SAML.
Even if you’re an established business and have developer time to spare, because of the security concerns, it’s crucial to build SAML correctly. This isn’t a one-and-done project either, SAML needs to be consistently updated as new IdPs will be created and customer submit their requests.
Why Choose PropelAuth’s SAML?
If you’ve decided to use a service provider, there’s a number of factors to consider such as price, difficulty of implementation, and on-going support. With PropelAuth, SAML is self-service, affordable, and comprehensive.
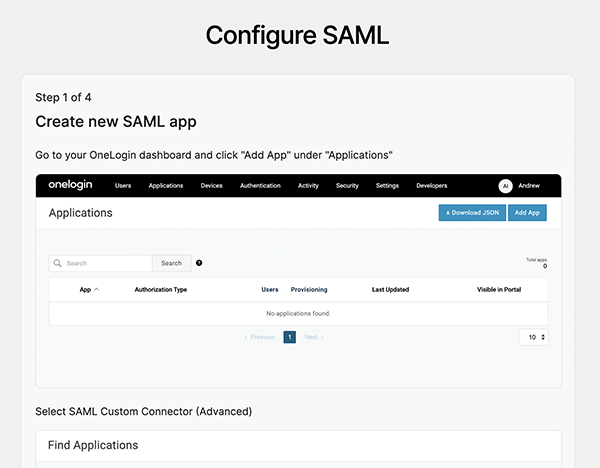
Self-service means ready to go as soon as you sign up. You can turn on SAML for your users with a toggle of a button on your dashboard. And for your customers, our wizards guide them through the set up process step-by-step. They’ll be able to configure their IdP on their own without needing to ask your support team for help.
Not only will working with us save you months of developer time in the beginning, we’re in it for the long haul. We support every major IdP and are continuously adding new providers as they emerge. And while we’ve designed every aspect of our product to be self-service, if you do have questions, you can reach out to us via email or shared slack room.
We’re also committed to ensuring SAML is accessible to a range of companies—not just large companies with giant budgets. Other providers up-charge for each SAML connection, but we believe you shouldn’t have to be an enterprise already in order to sell to other enterprises. SAML is available as part of our Growth tier, which you can learn more about here.
Ready to get started with SAML? Sign up here.


